What are Link's integrity and crossorigin attributes?
You might have seen these attributes when included Bootstrap CSS styles on your page, but why? Let's find out what are Link's Integrity and Crossorigin!
Bootstrap is the most popular framework for creating high-performance mobile sites based on CDN and start page templates in the world. When implementing specific scenarios, however, you may encounter some unfamiliar attributes. Let's take a look at two particular instances - Integrity and Crossorigin.
Integrity Attribute - What you need it?
The main point of using the Integrity attribute is boosting network security. The thing is, when connecting to a website based on one of the CDN servers via browser for the first time, users aren't able to verify whether the source of the loaded data is malicious or not.
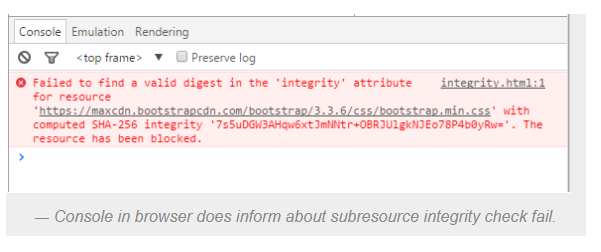
Technically, the Integrity attribute helps with just that - it enables the proper verification of the data source. That is, it merely allows the browser to verify the numbers in the right source file with the amounts requested by the source file located on the CDN server.
Going a bit deeper, in case of the established encrypted hash value of this source and its checked compliance with a predefined value in the browser - the code executes, and the user request is successfully processed.
Thus, the end-user knows for sure that network fraudsters didn't replace the source; this is a very relevant software measure when it comes to data sources hacked within CDN servers.
As a developer with this attribute in hand, you get many opportunities to check the integrity of data sources on the server-side. However, it's essential to remember that some older versions of web browsers don't support it and should also be adjusted every time the data source changes.
CrossOrigin Attribute - What is Its Place in Your Code?
Now for a crossorigin attribute. It helps developers optimize the rates of CDN performance, at the same time, protecting the website code from malicious scripts.
In particular, Crossorigin downloads the program code of the site in anonymous mode, without downloading cookies or performing the authentication procedure. This way, it prevents the leak of user data when you first load the site on a specific CDN server, which network fraudsters can easily replace addresses.
The attribute has two additional parameters: anonymous, which determines that requests for the downloadable item won't require cookies, and use-credentials, which allows secure data transfer during user authentication.
Bottom Line
Today, almost all websites use external sources of data. That's why web developers must make sure hackers don't tunnel these file sources that can potentially harm user data and overall experience.
Otherwise, some nasty situations may occur, like payment info and credentials theft, personal account hacking; you name it.
Both Integrity and Crossorigin come to the rescue of insightful web experts here. Using them is a surefire way to verify external sources and manage the downloading of cookie files, boosting the site's reliability and protection.
